Services > Use case
Eradicate the “Silo Tax”: The Executive Blueprint for Unified Cyber-Fraud Leadership.
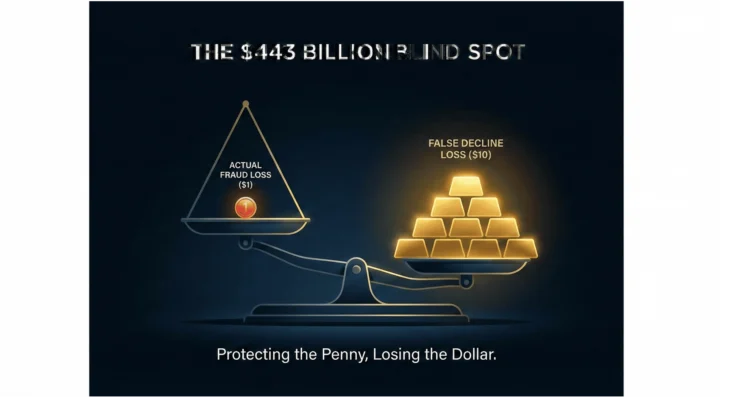
Close the execution gap between your Security, Fraud, and Finance teams with a formal Cyber-Fraud Trust Architecture™ —transforming disjointed liability into a board-ready, ROI-driven governance model.